I. Introduction: Why Vault Matters in the Modern DevOps World
In today’s cloud-native and multi-cloud era, secrets are everywhere—API tokens, database credentials, TLS certificates, encryption keys. Managing them securely can mean the difference between a resilient enterprise and a headline-making breach.
HashiCorp Vault has become the gold standard for secrets management. With Vault, organizations can:
- Centralize username/password storage for apps and services.
- Dynamically generate database credentials with limited TTLs.
- Securely store and rotate encryption keys.
- Issue and manage TLS certificates on demand.
But Vault doesn’t just protect secrets—it protects itself. That’s where Seal and Unseal operations come into play.
II. Core Components of HashiCorp Vault
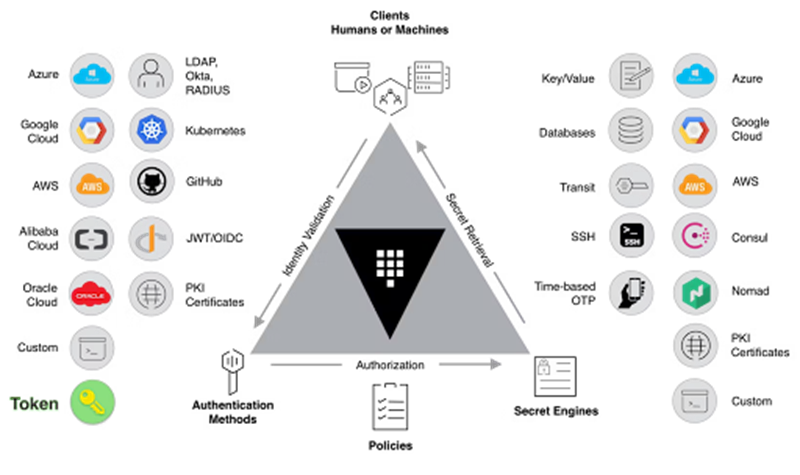
Before diving into Seal/Unseal, let’s quickly recap Vault’s main building blocks:
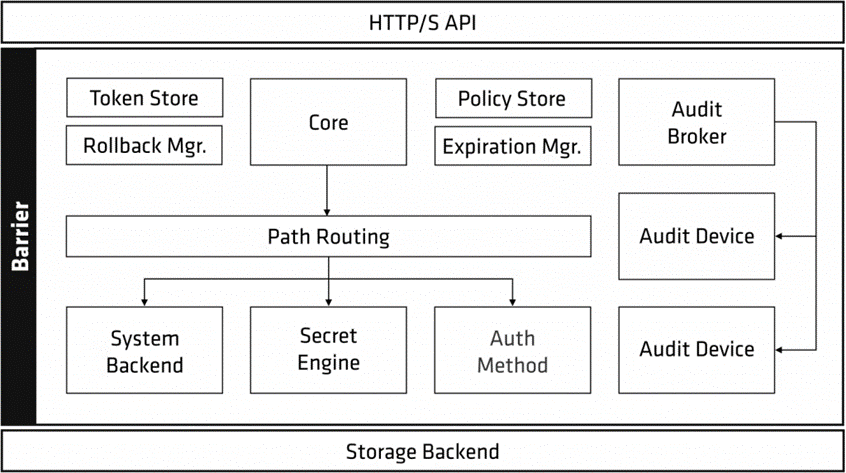
- Backend Storage
- Where Vault persists encrypted data (e.g., Consul, Raft, DynamoDB, or cloud storage backends).
- Data is always encrypted before hitting disk.
- Secrets Engine
- The heart of Vault—plugins that manage secrets.
- Examples: KV (key/value store), AWS/GCP/Azure engines, PKI engine for certificates, Transit engine for encryption-as-a-service.
- Auth Methods
- Define how apps and humans authenticate into Vault.
- Options: AppRole, Kubernetes, LDAP, GitHub, AWS IAM, etc.
- Audit Devices
- Provide a tamper-evident log of every request to Vault.
- Essential for compliance and troubleshooting.
III. The Seal/Unseal Mechanism Explained
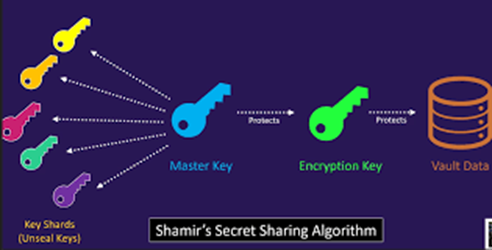
Vault never writes secrets in plaintext. Instead, it uses a two-layer encryption model:
- Data Encryption Key (DEK): Encrypts all secrets before persisting to backend storage.
- Root Key (a.k.a. Master Key): Encrypts the DEK itself.
When Vault starts, it begins in a sealed state:
- The DEK is encrypted on disk.
- The Root Key is needed to decrypt it.
- Without the Root Key, Vault cannot access any data.
Unseal Methods:
- Manual Unseal (Key Sharding with Shamir’s Secret Sharing)
- When initializing a Vault cluster, the Root Key is split into multiple Unseal Keys.
- You define:
- n = total number of keys generated.
- m = threshold of keys required to reconstruct the Root Key
- Example: n=5, m=3. Any 3 of the 5 keys can reconstruct the Root Key and unseal Vault.
- Keys are distributed to trusted organization members.
- Auto Unseal with External KMS/HSM
- Root Key is managed by a trusted hardware or cloud KMS (AWS KMS, Azure Key Vault, GCP KMS, or an HSM).
- Vault automatically contacts the KMS/HSM on restart to retrieve the Root Key.
- Simplifies ops in production but requires cloud/hardware integration.
- Auto Unseal with Transit Secrets Engine
- Uses another Vault cluster to hold a transit key dedicated for unseal.
This creates a layered architecture where one Vault can bootstrap another.
IV. Hands-On: Manual Unseal with Key Sharding
Step 1: Initialize the Cluster
1/Vault Before Initialization:
Right after installation and the very first startup, Vault is in an uninitialized state. If you run:
vault status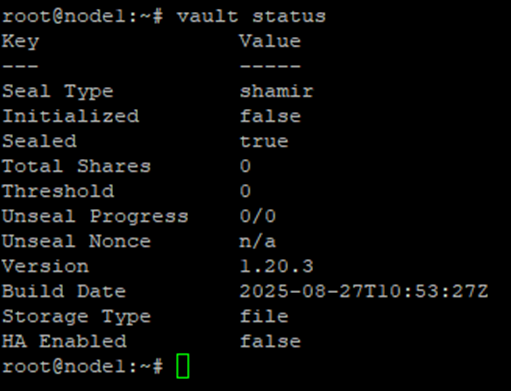
Initialized: false → Vault has not been initialized yet, no Root Key or Unseal Keys exist.
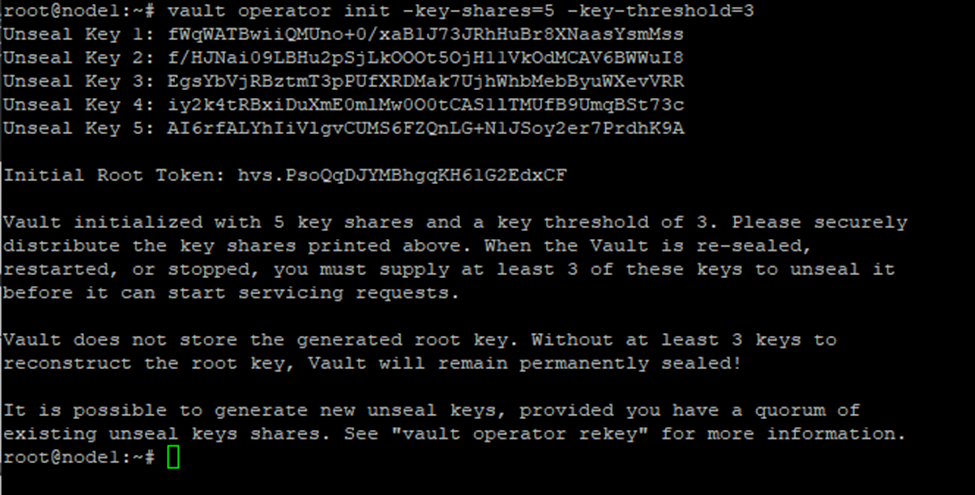
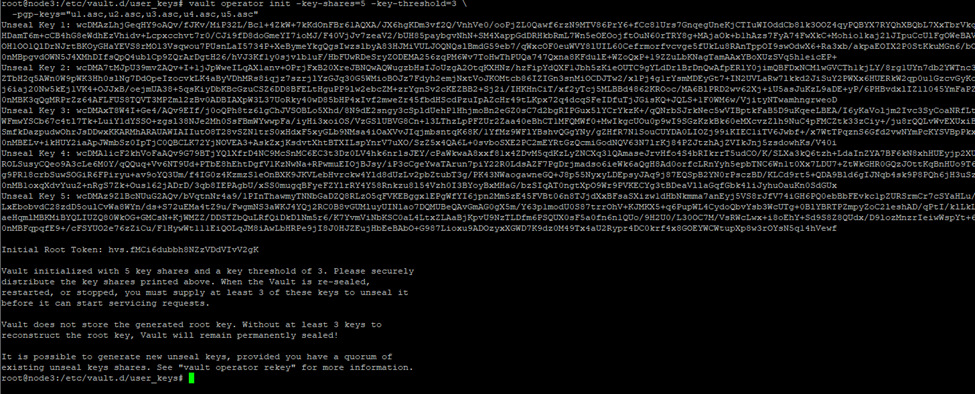
2/Initialize Vault with 5 key shares and a threshold of 3:
vault operator init -key-shares=5 -key-threshold=3
The output shows:
- 5 Unseal Keys (distribute them to different members).
- A Root Token (for initial admin setup).
Step 2: Check Vault Status
Immediately after initialization, Vault is still sealed. Run:
vault status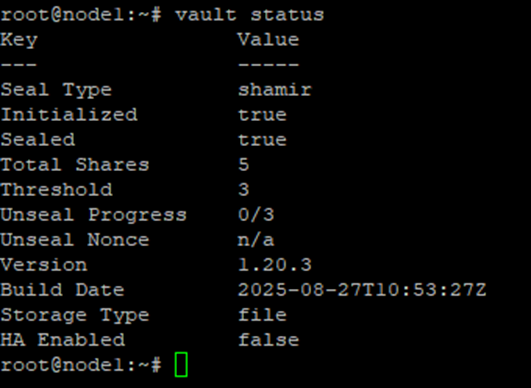
Explanation:
- Seal Type:
shamir→ Vault is using Shamir’s Secret Sharing. - Initialized:
true→ Vault has been set up. - Sealed:
true→ Vault is still locked; secrets inaccessible. - Total Shares:
5→ Total number of Unseal Keys generated. - Threshold:
3→ Minimum keys required to reconstruct the Root Key. - Unseal Progress:
0/3→ No keys have been entered yet. - Storage Type: Backend storage in use (e.g., Raft).
Step 3: Manual Unseal
Each trusted member provides their Unseal Key:
vault operator unseal <unseal_key_1>
vault operator unseal <unseal_key_2>
vault operator unseal <unseal_key_3>Member 1:
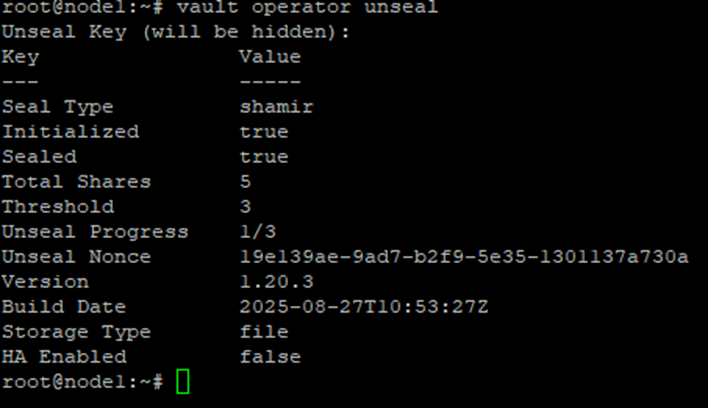
Member 2:
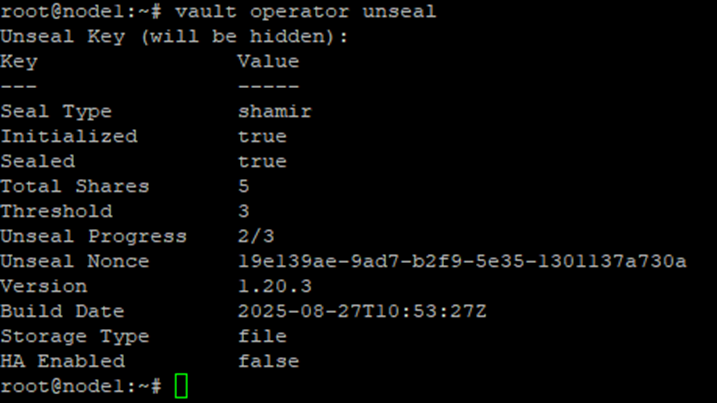
Member 3:
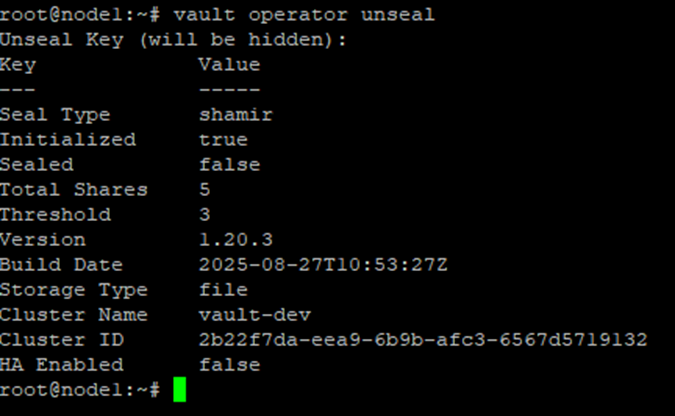
After the 3rd key, Vault transitions to unsealed state, and secrets can be accessed.
Security Concern: The Admin Risk
During vault operator init, all Unseal Keys are displayed on the admin’s terminal.
- Risk: The admin has visibility of every shard.
- Threat: Keys can be photographed, screen-captured, or compromised.
Step 1: Hardening with PGP Encryption
To mitigate the risk, Vault supports encrypting Unseal Keys with PGP public keys.
1/Each member generates a GPG keypair
sudo gpg --gen-key
sudo gpg --armor --export <member_email> > member.asc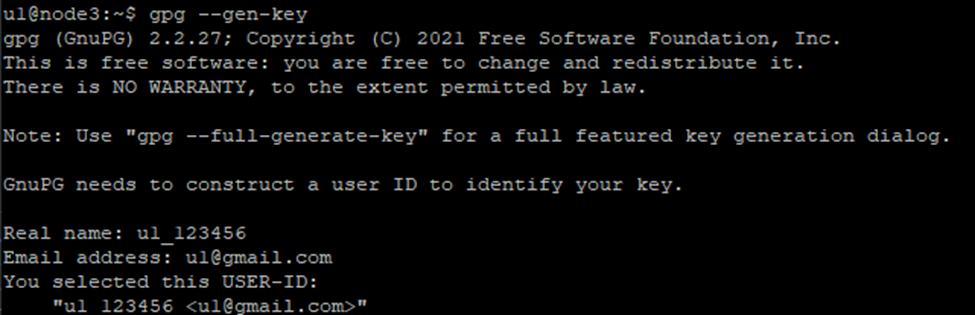
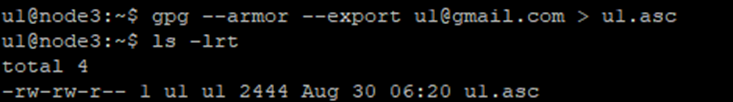
2/Members send .asc public key files to the admin
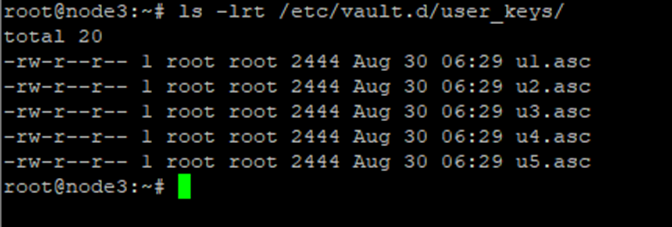
3/Admin initializes Vault with the PGP keys
vault operator init -key-shares=5 -key-threshold=3 \
-pgp-keys="member1.asc,member2.asc,member3.asc,member4.asc,member5.asc"4/Vault outputs PGP-encrypted Unseal Keys. Admin cannot see the plaintext keys
5/Each member decrypts their shard with their private key
export GPG_TTY=$(tty)
echo "<encrypted_shard>" | base64 --decode | gpg --decrypt;echoDuring this process, the member will be prompted to enter the passphrase that protects their private key (the one they set when generating the key pair). Once the passphrase is entered correctly, the command outputs the plaintext Unseal Key belonging to that member.
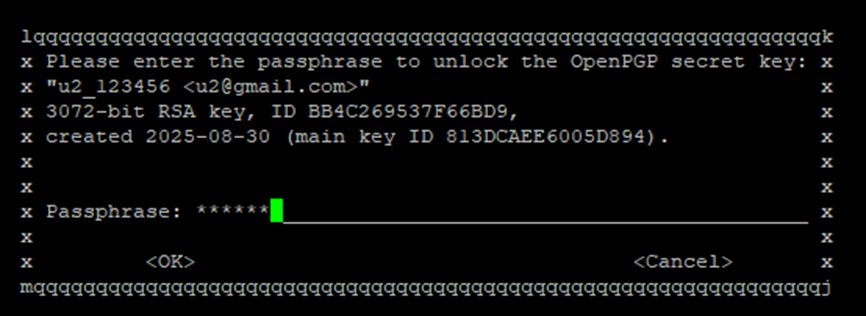
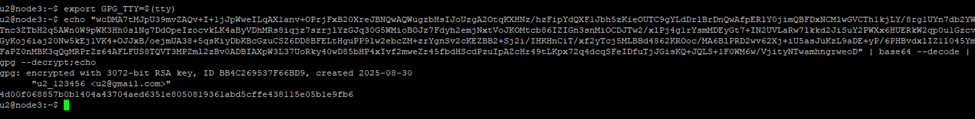
Now each member holds their real Unseal Key safely.
Step 2: Unseal Vault with Decrypted Unseal Keys
Once members decrypt their shards, they provide their real Unseal Keys to unseal the cluster:
vault operator unseal <member1_real_unseal_key>
vault operator unseal <member2_real_unseal_key>
vault operator unseal <member3_real_unseal_key>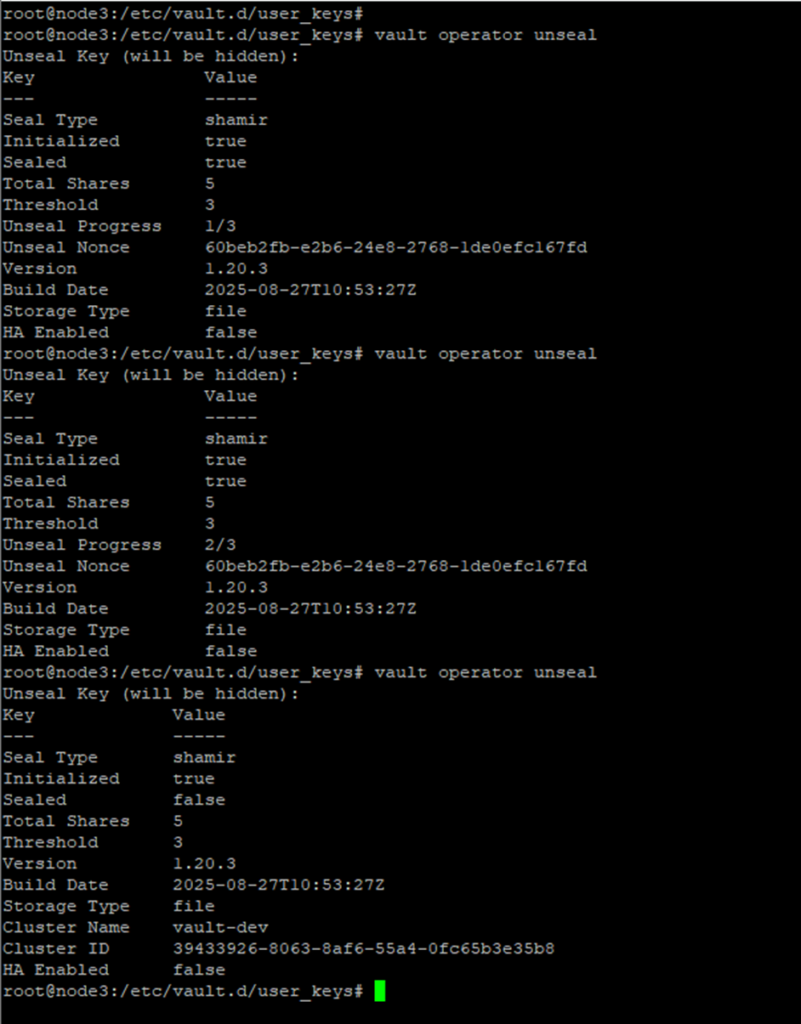
After 3 valid keys, Vault is fully unsealed and Vault is now open for use
Demo Recap:
- Cluster initialized: 5 key shares, threshold 3.
- Manual unseal: 3 members combine keys to reconstruct the Root Key.
- Hardened with PGP: Keys are safely delivered without the admin ever knowing them.
V. Conclusion
The Seal/Unseal mechanism is the backbone of Vault’s zero-trust philosophy.
- Manual unseal with Shamir’s Secret Sharing ensures that no single person controls Vault’s master secret.
- Using PGP encryption enhances this model by reducing insider risk.
- While enterprises may prefer Auto Unseal with HSM/KMS for operational efficiency, manual sharding remains invaluable for regulated environments, disaster recovery, and secure multi-party control.
Vault is not just a secrets manager—it’s a trust framework. And mastering Seal/Unseal is the first step in wielding Vault responsibly.
“PGP + Shamir = like giving everyone a piece of cake, but you still need three forks to eat it.”
Explore more insights on enterprise protection in our security topic at: