Explore Cloud, DevOps,System, Automation & Security — Without the Stress
Welcome to TechNoStress
TechNoStress is a blog dedicated to breaking down complex technology topics into clear, practical, and stress-free insights. Whether you’re just starting out or deep into the IT world, you’ll find tutorials, guides, and ideas to help you navigate Cloud, DevOps, Automation, and Security with ease.

Popular Categories
🔥 Most Read Articles
Cloud Insights
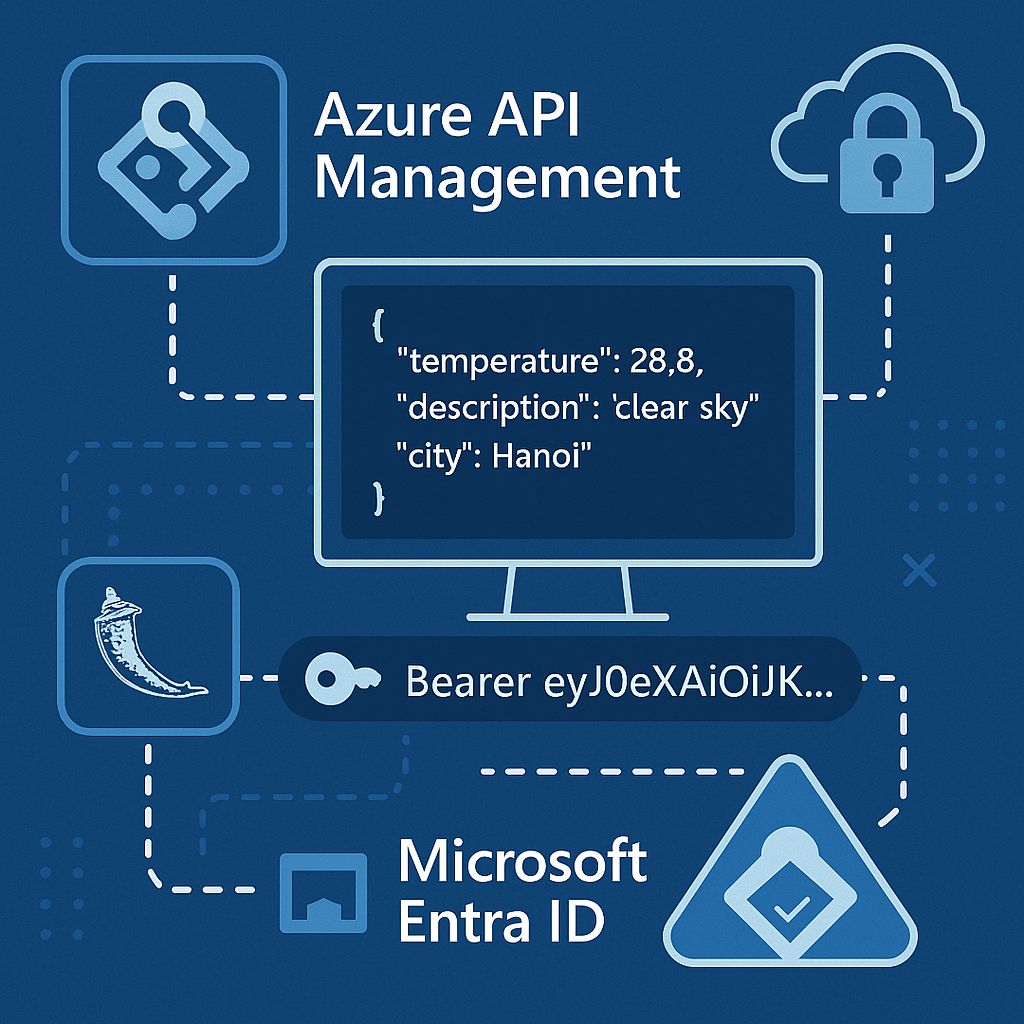
Cloud-Native API Security Done Right: Azure API Management + Entra ID for Your Flask Weather App
Unlock true cloud-native API security! Learn how to deploy, expose, and protect your Flask Weather…
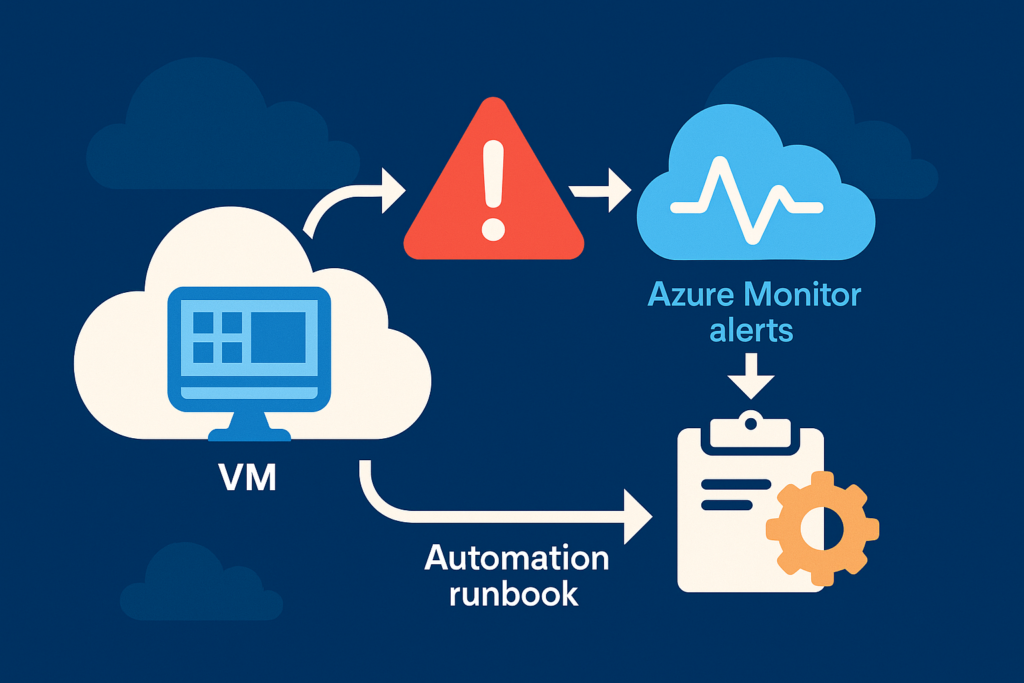
Build a Self-Healing Azure VM: Alerts + Automation Runbooks Step-by-Step
Learn how to create a fully automated self-healing Azure environment by combining VM monitoring with…
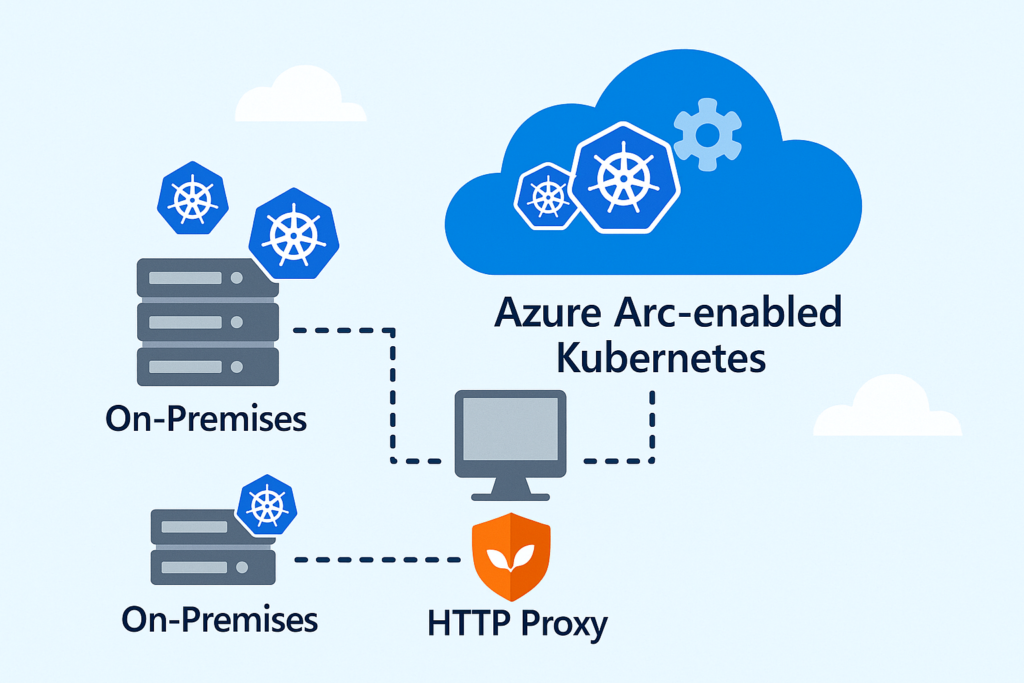
Mastering Azure Arc-enabled Kubernetes: Hybrid Power, Real Enterprise Use Cases
Master Azure Arc-enabled Kubernetes with real-world enterprise use cases and a hands-on lab that simulates…
Cloud-Init on Azure: Auto-Provision a Flask App Right After VM Creation
Spin up an Azure VM and auto-deploy your Flask app in minutes—no manual setup needed.
This…
System Essentials
Mastering Azure Arc-enabled Kubernetes: Hybrid Power, Real Enterprise Use Cases
Master Azure Arc-enabled Kubernetes with real-world enterprise use cases and a hands-on lab that simulates…
Effortless Elasticsearch Backups: Automate Snapshots to S3 with Python in Minutes
Automate Elasticsearch backups to any S3-compatible storage using Python. A simple, efficient guide to set…
From Tickets to Clicks: Building a Zero-License Self-Service VM Portal on vSphere with Ansible AWX
Learn how to transition from a traditional process to an efficient self-service system with Ansible…
Import CSV Data to Azure SQL Server Using Python
A step-by-step tutorial on importing CSV files into Azure SQL Server with Python, covering setup,…
DevOps in Action
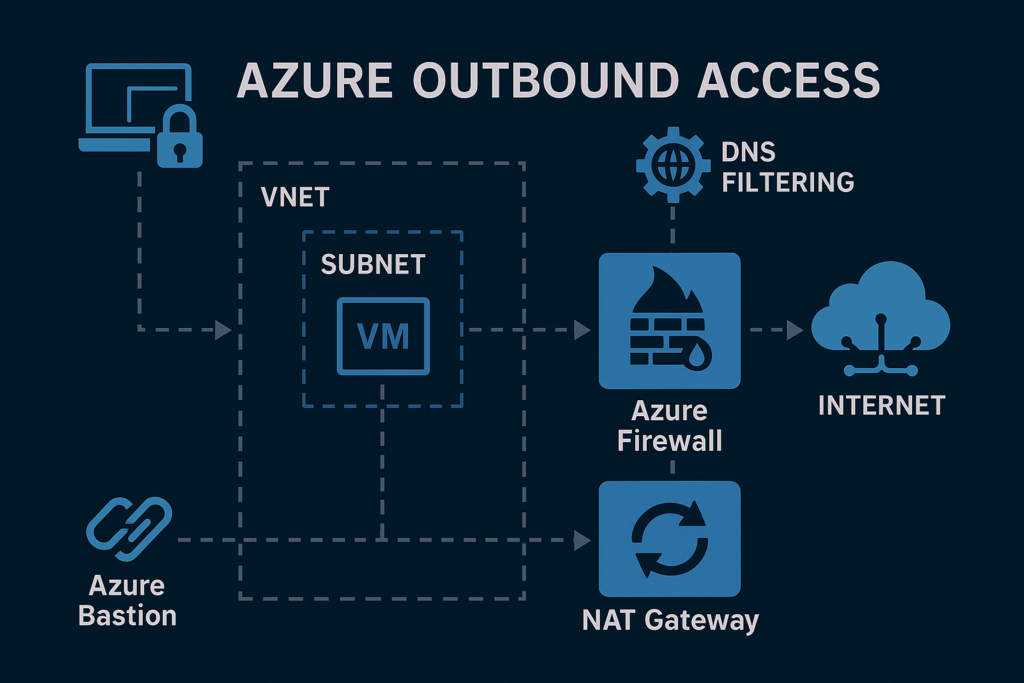
Azure Outbound Access Done Right: FQDN Filtering, NAT Scaling, and Bastion Integration
Discover how to build secure, policy-controlled outbound internet access in Azure — without using public…
Cloud-Native API Security Done Right: Azure API Management + Entra ID for Your Flask Weather App
Unlock true cloud-native API security! Learn how to deploy, expose, and protect your Flask Weather…
Fixing memcache.go:265 After Renewing Expired Kubernetes Certs with kubeadm
Ran kubeadm certs renew all and suddenly locked out of your cluster? Don’t panic —…
🌐 Mastering IP Visibility in Azure: Automating Cloud-to-IPAM Sync for Hybrid Success
Struggling to keep up with IP addresses in Azure? Learn how to automatically scan, track,…
Automate Everything — Smartly
Effortless Elasticsearch Backups: Automate Snapshots to S3 with Python in Minutes
Automate Elasticsearch backups to any S3-compatible storage using Python. A simple, efficient guide to set…
Build a Self-Healing Azure VM: Alerts + Automation Runbooks Step-by-Step
Learn how to create a fully automated self-healing Azure environment by combining VM monitoring with…
Cloud-Init on Azure: Auto-Provision a Flask App Right After VM Creation
Spin up an Azure VM and auto-deploy your Flask app in minutes—no manual setup needed.
This…
🌐 Mastering IP Visibility in Azure: Automating Cloud-to-IPAM Sync for Hybrid Success
Struggling to keep up with IP addresses in Azure? Learn how to automatically scan, track,…
Cybersecurity, DevSecOps & Best Practices
OS Command Injection in Web Apps: Risks, Detection, and Prevention
Discover how OS command injection vulnerabilities arise in Python web applications, how attackers exploit them…
Unsealing HashiCorp Vault Secure Way: Shamir + PGP
Learn how to securely unseal HashiCorp Vault using Shamir’s Secret Sharing with PGP-encrypted key shards….
Building an AI-Powered Log Analyst: Running Google LLM Gemma Model To Detect Linux Server Anomalies
Discover how to transform raw Linux server logs into smart insights with an AI-powered log…
Automating Network Security: Shell Scripting to Detect Devices, Open Ports & Send Alerts
Use shell scripting to automate network scans, detect new devices, and send instant email alerts…